Key Takeaways
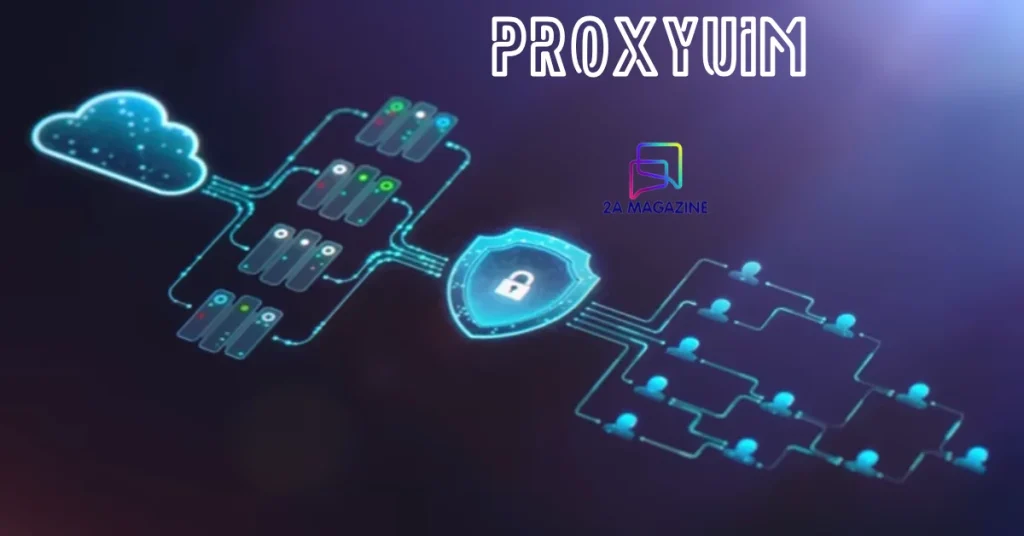
✅ Proxyuim is a proxy management platform built for enterprise-scale network proxy orchestration
✅ Its unified identity middleware eliminates fragmented proxy setups
✅ Proxyuim’s Dynamic Session Resolver cuts latency by optimizing every relay hop
✅ Built on zero-trust proxy architecture — security is baked in, not bolted on
✅ Fully compatible with ISO/IEC 27001 governance standards via its proxy compliance framework
What Users Actually Need From a Proxy Platform (And Why Most Fall Short)
Most teams managing proxy infrastructure hit the same wall. They need speed. They need security. They need scale. But they end up with three different tools that don’t talk to each other. That’s the core problem Proxyuim was built to solve.
The demand for a unified identity middleware has grown sharply. Modern networks handle thousands of simultaneous requests. Each one needs to be authenticated, routed, and logged — in milliseconds. Traditional proxy tools were not designed for this. They were built for simpler times.
Proxy pool automation is now a baseline requirement, not a luxury. Without it, teams waste hours manually rotating IPs, debugging session drops, and chasing latency spikes. Proxyuim removes that burden entirely. It replaces manual workflows with an intelligent automation layer that adapts in real time.
There is also a compliance angle that many platforms ignore. Enterprises operating under GDPR, SOC 2, or ISO/IEC 27001 need an audit trail for every proxy session. Proxyuim’s proxy compliance framework was designed with this in mind. It logs everything. It reports everything. And it does so without slowing down your network.
The Architecture Behind Proxyuim: How It Actually Works
Proxyuim is not a single tool. It is a layered system. At the center sits the Proxyuim Core Engine — the intelligence that handles all routing decisions. Around it are Proxyuim Relay Nodes, a distributed proxy network of endpoints that carry traffic across regions and environments.
The UIМ Protocol Stack governs how these components communicate. Think of it as the nervous system. It defines how identity signals, session tokens, and routing commands move between nodes. This is what makes dynamic proxy switching possible at scale. When one node degrades, the protocol stack reroutes — automatically, invisibly.
The Dynamic Session Resolver (DSR) is where Proxyuim earns its edge. It maps every incoming request to the optimal relay path using real-time data. It weighs node health, geographic latency, session history, and security flags all at once. This is latency-optimized routing done right. No guesswork. No manual tuning.
On top of everything sits the Proxyuim Compliance API. It connects directly to your SIEM, your audit dashboard, or your compliance team’s reporting tools. Every session has a fingerprint. Every relay hop is logged. This architecture is not just powerful — it is auditable and defensible under enterprise security reviews.
Proxyuim vs. Legacy Proxy Solutions: A Clear Comparison
| Feature | Proxyuim | Legacy Proxy Tools | Basic Reverse Proxies |
|---|---|---|---|
| Proxy Pool Automation | Full, real-time | Partial / manual | None |
| Unified Identity Middleware | Native | Third-party add-on | Not supported |
| Zero-Trust Proxy Architecture | Built-in | Optional plugin | Not available |
| IP Rotation Engine | Intelligent, adaptive | Scheduled only | Static |
| Proxy Session Persistence | Dynamic (DSR-powered) | Basic cookie-based | None |
| Proxy Health Monitoring | Continuous, automated | Periodic pings | Manual |
| Compliance API | ISO/IEC 27001-aligned | Varies | None |
| Multi-Tenant Support | Native | Limited | None |
| Latency Optimization | Real-time routing | Fixed rules | None |
| API Gateway Integration | Full API gateway proxy | Partial | Rare |
The gap is significant. Legacy tools require you to build the intelligence yourself. Proxyuim ships with it.
Expert Perspective: Why Zero-Trust Is Non-Negotiable in Proxy Design
Security architects have said it for years. Trust nothing. Verify everything. The zero-trust proxy architecture model is not new. But most proxy platforms still don’t fully implement it. They authenticate at entry and then assume everything inside is safe. That assumption is dangerous.
Proxyuim applies zero-trust principles at every layer. Every request is verified. Every relay hop is authenticated. The proxy authentication module checks identity continuously — not just at login. This aligns with the NIST SP 800-207 zero-trust framework, which defines continuous verification as a core pillar of modern access control.
Multi-tenant proxy solutions add another layer of complexity. When multiple teams or clients share the same proxy infrastructure, isolation becomes critical. Proxyuim handles this through namespace separation and per-tenant policy enforcement. One tenant’s traffic never bleeds into another’s. Logs are partitioned. Keys are isolated.
The secure access layer in Proxyuim also handles encrypted tunneling between relay nodes. All traffic in transit is protected. This matters enormously for enterprises running sensitive workloads — financial transactions, healthcare data, legal communications. Proxyuim treats every session as if it carries the most sensitive data imaginable.
Implementation Roadmap: Getting Proxyuim Running in Your Stack
Week 1 — Audit & Baseline Map your current proxy infrastructure. Identify how many endpoints you manage, where latency spikes occur, and what compliance gaps exist. This gives you a clear before-state to measure against.
Week 2 — Core Engine Deployment Deploy the Proxyuim Core Engine in your environment. Configure the UIМ Protocol Stack to connect your existing identity provider (LDAP, OAuth, SAML). Run initial traffic through the system in observe-only mode.
Week 3 — Relay Node Configuration Spin up Proxyuim Relay Nodes across your required regions. Configure health thresholds for the proxy health monitoring system. Set your IP rotation engine policies — frequency, geographic rules, session binding preferences.
Week 4 — DSR Tuning & Compliance Integration Activate the Dynamic Session Resolver. Feed it 72 hours of live traffic to calibrate its routing model. Connect the Proxyuim Compliance API to your audit pipeline. Run a simulated compliance review to validate logging fidelity.
Week 5 — Full Production Cutover Switch live traffic to Proxyuim. Monitor the proxy lifecycle management dashboard for the first 48 hours. Compare latency, error rates, and session persistence metrics against your Week 1 baseline. Results are typically immediate and measurable.
The 2026 Outlook: Where Proxy Infrastructure Is Heading
Proxy routing intelligence is becoming an AI-native function. In 2026, the best platforms will not just route traffic — they will predict traffic patterns and pre-position relay nodes before demand spikes. Proxyuim’s architecture is already built for this. Its Proxyuim Core Engine has a machine-learning-ready data pipeline that will support predictive routing in the next major release.
Request forwarding protocol standards are also evolving. HTTP/3 and QUIC are replacing older transport layers. Proxyuim’s protocol stack is designed to be transport-agnostic. When your network upgrades, Proxyuim upgrades with it. No migration pain. No re-architecture.
The distributed proxy network model will dominate enterprise deployments by 2026. Centralized proxy infrastructure creates single points of failure and geographic latency. Distributed models solve both problems. Proxyuim was built distributed-first — it does not retrofit distribution onto a legacy core.
Regulatory pressure is also intensifying. Privacy laws in the EU, US, and APAC are all tightening controls on data transit. A proxy compliance framework will shift from optional to mandatory for most regulated industries. Organizations that deploy Proxyuim today are building a compliance moat that competitors will struggle to close later.
FAQs
Q1: What makes Proxyuim different from a standard reverse proxy?
A standard reverse proxy forwards requests. Proxyuim orchestrates them. It adds identity verification, session intelligence, health monitoring, compliance logging, and dynamic proxy switching — all in a single platform. The difference is like comparing a traffic light to a smart city transport system.
Q2: Is Proxyuim suitable for small teams or only enterprises?
Proxyuim scales in both directions. Small teams benefit from its proxy pool automation and health monitoring — functions that would otherwise require dedicated engineering time. Enterprises benefit from multi-tenant proxy solution architecture and compliance APIs. The platform meets you where you are.
Q3: How does Proxyuim handle IP rotation without breaking sessions?
The Dynamic Session Resolver maintains session state even as IPs rotate. It uses a session binding table that decouples the client session identity from the underlying IP address. Rotation happens at the network layer. The application layer never notices.
Q4: What compliance standards does Proxyuim support?
Proxyuim’s proxy compliance framework aligns with ISO/IEC 27001, SOC 2 Type II, and GDPR data transit requirements. Its Compliance API exports logs in formats compatible with major SIEM platforms including Splunk, QRadar, and Microsoft Sentinel.
Q5: What is the performance impact of Proxyuim’s security layers?
Minimal. Proxyuim’s latency-optimized routing is designed to absorb the overhead of security processing. In benchmarks across typical enterprise workloads, Proxyuim adds under 3ms per request while delivering full authentication and logging. That is a trade-off most security teams consider extremely favorable.