Ransomware attacks against manufacturers are no longer isolated incidents—they have become structured, repeatable operations executed with precision. For cybersecurity professionals and business leaders alike, understanding how these attacks or manufacturing ransomware attack unfold is critical to defending against them.
Unlike opportunistic attacks targeting individual users, ransomware campaigns against manufacturing organizations are often deliberate and methodical. Attackers study environments, identify weaknesses, and move through networks in stages—often remaining undetected until the final payload is deployed.
To effectively mitigate risk, manufacturers must first understand the anatomy of these attacks.
Stage 1: Initial Access — The Entry Point
Every ransomware attack begins with a foothold.
In manufacturing environments, initial access is commonly achieved through:
- Phishing emails targeting employees
- Compromised remote desktop (RDP) access
- Stolen VPN credentials
- Exploitation of unpatched internet-facing systems
Attackers increasingly rely on credential theft rather than brute-force entry. Once valid login credentials are obtained, they can often bypass traditional perimeter defenses entirely.
In many cases, attackers do not trigger alarms at this stage. Instead, they establish persistence and begin quietly mapping the environment manufacturing ransomware attack.
Stage 2: Establishing Persistence and Privilege Escalation
After gaining access, attackers focus on maintaining control and escalating their privileges within the network.
This phase often includes:
- Installing backdoors or remote access tools
- Harvesting additional credentials
- Exploiting misconfigured permissions
- Escalating privileges to administrative accounts
Manufacturing environments are particularly vulnerable here due to inconsistent identity management practices across IT and operational systems manufacturing ransomware attack.
Once administrative access is achieved, attackers effectively gain control over large portions of the network.
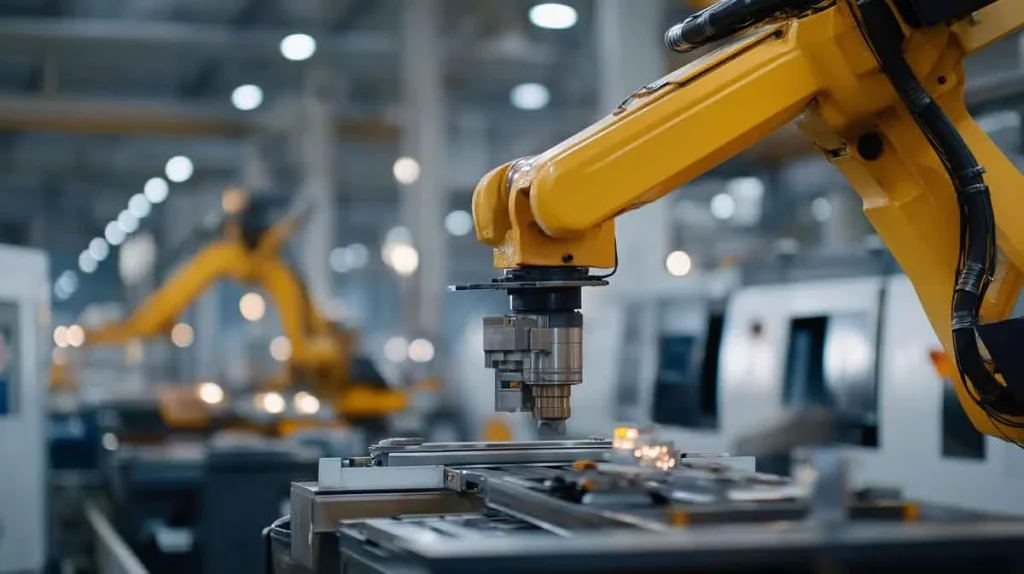
Stage 3: Lateral Movement — Crossing from IT to OT
One of the most critical—and dangerous—phases of a manufacturing ransomware attack is lateral movement.
Attackers move from system to system, often starting in corporate IT environments before targeting operational technology (OT), including:
- Industrial control systems (ICS)
- Supervisory control and data acquisition (SCADA) systems
- Production line controllers
In many manufacturing networks, segmentation between IT and OT environments is limited or poorly enforced. This allows attackers to pivot from user workstations into production environments.
Once inside OT systems, the potential for operational disruption increases significantly.
Stage 4: Data Exfiltration — The Double Extortion Model
Modern ransomware attacks are no longer limited to encrypting files.
Before deploying ransomware, attackers often:
- Identify sensitive data repositories
- Exfiltrate intellectual property
- Extract financial and operational data
This enables a “double extortion” strategy, where organizations face two simultaneous threats:
- Loss of access to critical systems
- Public exposure of sensitive data
For manufacturers, this can include proprietary designs, supplier agreements, and customer information—assets that extend far beyond immediate operational impact.
Stage 5: Payload Deployment — Operational Disruption
The final stage is where the attack becomes visible.
Attackers deploy ransomware across the network, encrypting systems and rendering them inaccessible. In some cases, destructive malware is used to wipe devices entirely.
For manufacturers, this often results in:
- Halted production lines
- Disabled machinery interfaces
- Inaccessible scheduling and logistics systems
Because manufacturing relies on real-time coordination, even a short disruption can cascade into significant operational and financial consequences.
Stage 6: Extortion and Negotiation
Once systems are locked, attackers initiate contact.
Ransom demands are typically accompanied by:
- Proof of stolen data
- Deadlines for payment
- Threats of public data release
At this stage, organizations must make critical decisions under pressure—balancing recovery timelines, financial costs, and reputational risk.
Some organizations rely on internal teams, while others engage an external IT Service Provider to assist with containment, investigation, and recovery.
Why Manufacturing Is Uniquely Vulnerable
The structure of manufacturing environments makes them particularly susceptible to ransomware attacks.
Key risk factors include:
- Legacy systems that cannot be easily patched
- Flat networks with limited segmentation
- High reliance on uptime and operational continuity
- Complex supply chains and third-party integrations
These factors create an environment where attackers can move quickly and where the cost of disruption is exceptionally high.
Lessons from the Field
Across multiple real-world incidents, a consistent pattern emerges: ransomware attacks succeed not because of a single failure, but because of a series of small gaps that align.
Common contributing factors include:
- Lack of multi-factor authentication
- Insufficient network segmentation
- Limited visibility into OT environments
- Inadequate incident response planning
Organizations that address these gaps proactively are significantly more resilient when attacks occur.
Building a More Resilient Manufacturing Environment
Defending against ransomware requires a layered and proactive approach.
Manufacturers should prioritize:
- Strong identity and access controls
- Continuous monitoring of endpoints and networks
- Segmentation between IT and OT systems
- Regular backup and recovery testing
- Employee awareness and phishing training
Equally important is the ability to detect and respond to threats quickly. The faster an organization can identify suspicious activity, the more effectively it can limit the impact.
Final Thoughts
Ransomware attacks on manufacturing organizations are not random—they are engineered.
By understanding the stages of an attack, organizations can better anticipate how threats develop and where to focus defensive efforts.
In an increasingly connected and high-stakes industrial environment, cybersecurity is no longer just a technical concern. It is a fundamental component of operational resilience.
For manufacturers, the ability to withstand and recover from cyberattacks will increasingly define long-term success.
About the Author
Matt Kahle is President and Co-Owner of Real IT Solutions, a Michigan-based managed IT services provider specializing in cybersecurity, risk management, and proactive technology strategy. He works closely with manufacturing organizations to strengthen security posture and protect critical operations.
A high-impact guide designed for serious results at 2A Magazine.